Jun 15, 2012
Quantum cryptography? Pah! That’s for newbies, according to researchers from Texas A&M University who claim to have pioneered unbreakable cryptography based on the laws of thermodynamics; classical physics, rather than quantum.
For almost as long as I’ve been into bleeding edge technology, quantum cryptography has hovered in the wings, threatening with a moment’s notice to sweep in and completely revolutionize secure networking. In theory, quantum crypto (based on the laws of quantum mechanics) can guarantee the complete secrecy of transmitted messages: To spy upon a quantum-encrypted message would irrevocably change the content of the message, thus making the messages unbreakable. In practice, though, while the communication of the quantum-encrypted messages is secure, the machines on either end of the link can never be guaranteed to be flawless. For example, what good is a quantum communication channel if the transmitted (or received) message is stored in local memory that can be easily cracked?
According to Laszlo Kish and his team from Texas A&M, however, there is a way to build a completely secure end-to-end system — but instead of using quantum mechanics, you have to use classical physics: the second law of thermodynamics, to be exact. The second law of thermodynamics deals with continued entropy; the idea that, over time, a system will always lose energy to its environment. It is this effect that will eventually lead to an incredibly sparse spread of energy, and the death of the universe.
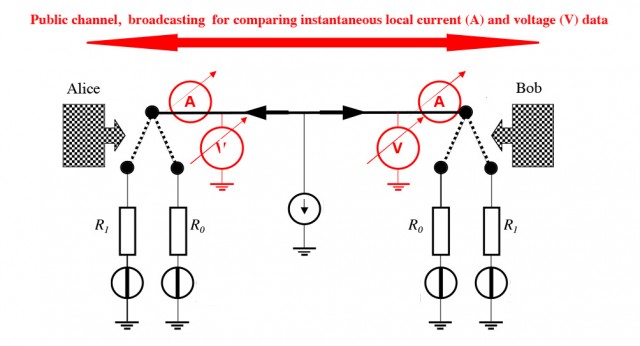
But back to cryptography. Kish’s system is made up of a wire (the communication channel), and two resistors on each end (one representing binary 0, the other binary 1). Attached to the wire is a power source that has been treated with Johnson-Nyquist noise (thermal noise). Johnson noise is often the basis for creating random numbers with computer hardware.
When Alice wants to send a message to Bob, she encodes her message by modulating the power source using the two resistors at her end of the wire — if she wants to send a binary 0, she connects the first resistor to the wire; binary 1, the other resistor. The result is a signal that still appears to be Johnson noise, but which has had its current modulated by Alice. Bob connects his resistors at random, and then measures the signal that arrives at his end. Because both parties know the voltage and current of the power source, and Bob knows which resistor he has connected, he can analyze the voltage and current of the signal to work out which resistor Alice is using — and thus a binary message is transmitted.
Much like quantum crypto, spying (man-in-the-middle) attacks on this thermodynamic system are apparently impossible. If Eve happens to be listening to the communication, she doesn’t know which resistor was connected and thus can’t decrypt the Johnson noise. The second law of thermodynamics prevents Eve from extracting the information with a man-in-the-middle attack — and to actively interrogate Alice or Bob’s resistors would require the addition of more energy to the system, which can easily be spotted.
Kish and his team claim that this system is completely secure — a claim that so far hasn’t been rebutted. It’s incredibly unlikely that the system is unbreakable — but who knows! Rather significantly, there is also no mention of the max transmission distance of the signal (can it be repeated/amplified?) or the max data rate. Kish will be discussing his findings at the IEEE Workshop on Soft Computing Applications in August, so we should know more then.
Now read about quantum teleportation, and the latest advances in quantum computing
Read more at Technology Review, or check out the paper arXiv:1206.2534v2